SECURE END-TO-END IOT
COMMUNICATION
CASE STUDY
Secure End-to-End IoT Communication
challenge
While the transition to a more connected world gives rise to new possibilities, the correct handling of security and privacy issues is becoming increasingly important. CISC adds trust to our connected world by designing and implementing different protection schemes on hardware and software levels: from the sensor and actuator layers over smart gateways to the business logic and analytics level.

solution
Our products ensure secure generation, submission, storage, and access (use) of confidential data during the pre-personalization process of a connected device and during the runtime of its application. The products allow various protection schemes on different hardware and software layers.
SCALABLE CUSTOM PRE-CONFIGURATION
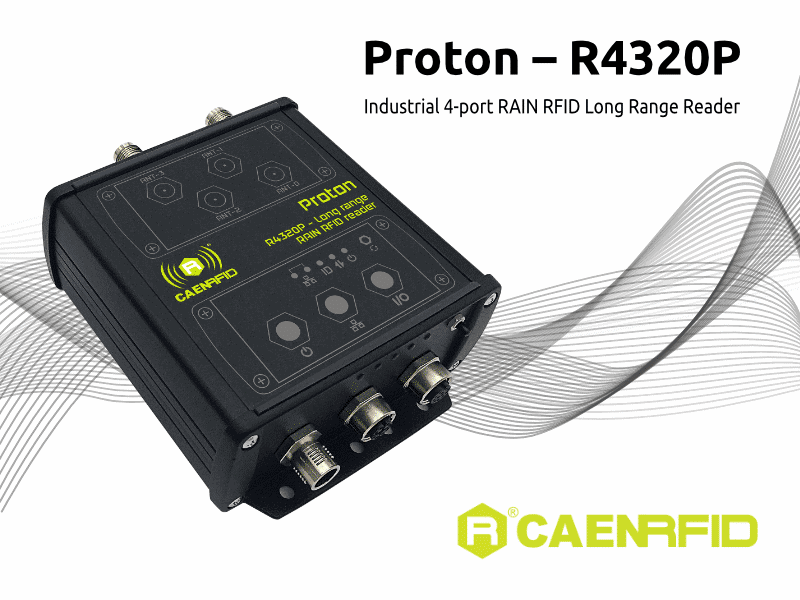
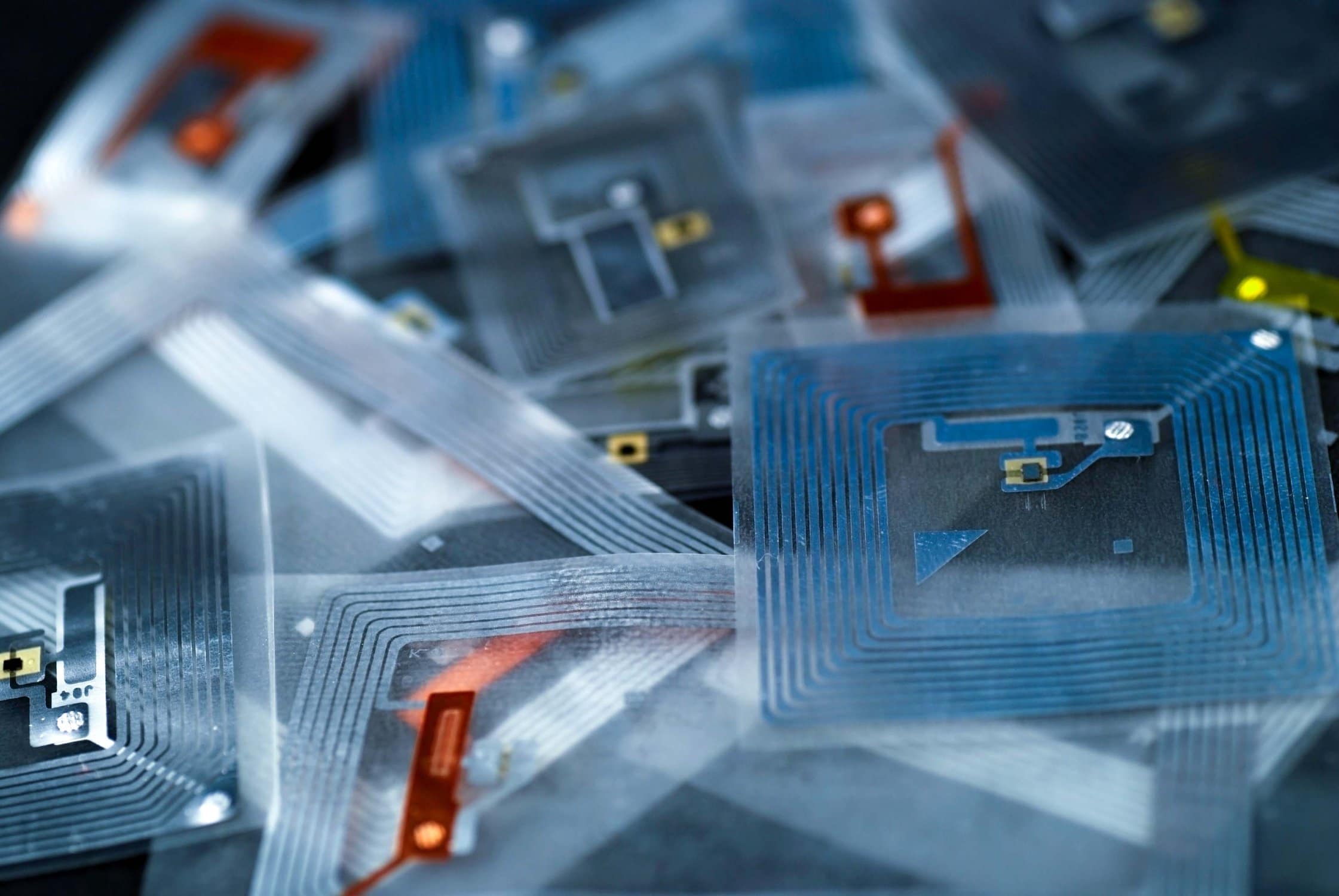
One of the most important steps is the device provisioning phase during the setup of the system. This is in most cases related to local deployment of your sensor device(s) or any other device to gather data from your system. “Your device” is to be considered as a device known by the entire system, can be pre configured in a secure and unique configuration process and encrypts data gathered and transmitted to the target endpoint by means of unique hardware keys. Custom provisioning processes enable us to adapt your devices to your needs and requirements.
- Connect your devices to the CISC service-framework
- Let us securely set up your device by taking into account multiple types of credentials
- Benefit from our scalability solutions for an automated provisioning scheme
SECURE YOUR APPLICATION AND DATA TRANSPORTATION
For securing the data packets transferred between different communication participants, the CISC-service-framework provides several security primitives, including symmetric and asymmetric cryptographic protection mechanisms, and tamper-safe storage. The plurality of wired and wireless standards generally poses troubles concerning the compatibility between collocated networks. Additionally, execution speed and energy consumption are additional factors that have to be taken into account. The CISC-service-framework is composed of a set of different communication drivers enabling wired and wireless communication according to your needs.
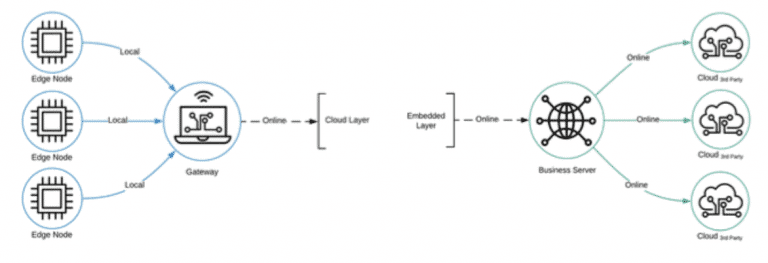
The simultaneous usage of local and online wireless data transmission techniques and the correct level of protection is essential to realize a secure data transfer between several devices of a distributed system. Use our product to securely connect different sensors for confidential data exchange. Car 4.0 engine test bench. Connected driving is a hot topic in the automotive industry and a leverage to push new Mobility as a Service (MaaS) methodologies, making vehicles an essential part of the Internet of Things (IoT). However, these new technologies often lead to security risks and privacy concerns, especially due to the increasing number of datasets exchanged between vehicles, drivers, and local infrastructure.
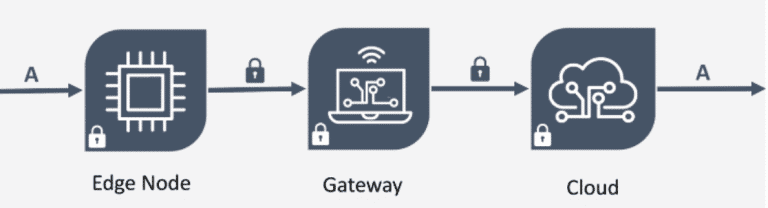
Enable end-to-end secured data aggregation and exchange through different IoT layers. The typical IoT data collection system includes devices from various IoT layers. While edge nodes act as data collectors, a dedicated gateway device enables communication to the cloud. End-to-end security is enforced with specialized hardware protection units where unique key material and certificates are stored and managed.